Crypto Wallet Apps Supporting Secure Storage And Transactions
Crypto wallet apps have become a foundational tool for anyone participating in the digital asset ecosystem. As cryptocurrencies move from speculative assets to instruments used for payments, decentralized finance, and long-term investment, the need for secure, reliable, and user-friendly storage solutions has never been greater. Modern wallet applications are no longer simple key holders; they are sophisticated platforms designed to balance accessibility with robust protection against theft, fraud, and operational mistakes.
TLDR: Crypto wallet apps provide secure storage and transaction capabilities for digital assets by protecting private keys and enabling blockchain interactions. The most reliable wallets combine strong encryption, multi-factor authentication, and user-controlled key management. There are different types of wallets—custodial, non-custodial, hot, and cold—each suited for specific risk profiles. Choosing the right wallet requires understanding security practices, transaction verification processes, and personal usage needs.
Contents
- 1 The Role of Crypto Wallet Apps
- 2 Understanding Wallet Types
- 3 Core Security Features of Modern Wallet Apps
- 4 Transaction Integrity and Verification
- 5 Integration with Decentralized Applications
- 6 Risk Management Best Practices for Users
- 7 Regulatory and Compliance Considerations
- 8 Evaluating a Crypto Wallet App
- 9 The Future of Secure Wallet Technology
- 10 Conclusion
The Role of Crypto Wallet Apps
At their core, crypto wallets do not actually “store” cryptocurrencies in the traditional sense. Digital assets remain on the blockchain. What wallets store are private keys, which allow users to access and authorize transactions involving their funds. Whoever controls the private key controls the assets.
A modern crypto wallet app serves several critical functions:
- Secure private key storage
- Transaction signing and broadcasting
- Balance monitoring across multiple blockchains
- Integration with decentralized applications (dApps)
- Backup and recovery mechanisms
The reliability of a wallet app directly affects the safety of a user’s holdings. Security architecture, transparency, and development standards are not optional enhancements—they are essential requirements.
Understanding Wallet Types
Crypto wallet apps can broadly be categorized into several types, each offering a different balance between convenience and security.
1. Custodial Wallets
Custodial wallets are managed by third-party platforms, such as exchanges. In this model, the provider controls the private keys on behalf of the user.
- Advantages: Ease of use, password recovery, integrated trading.
- Risks: Counterparty risk, exposure to exchange breaches.
Custodial solutions may be appropriate for beginners or high-frequency traders but are less suitable for long-term asset storage.
2. Non-Custodial Wallets
Non-custodial wallets give users exclusive control of their private keys. This model embodies the core principle of blockchain technology: self-sovereignty.

- Advantages: Full control over assets, reduced third-party risk.
- Risks: Responsibility for backup, no centralized recovery support.
Non-custodial wallets are often preferred by serious investors and users engaged in decentralized finance activities.
3. Hot vs. Cold Wallets
Wallets are also classified based on their internet connectivity:
- Hot wallets: Connected to the internet (mobile and desktop apps). Suitable for everyday use.
- Cold wallets: Offline storage solutions such as hardware devices. Ideal for long-term storage.
Many experienced users adopt a hybrid strategy, keeping smaller amounts in hot wallets for transactions while storing significant holdings offline.
Core Security Features of Modern Wallet Apps
Security is the defining attribute of a trustworthy crypto wallet app. Well-designed wallets incorporate multiple layers of protection.
Private Key Encryption
Private keys should be encrypted locally on the user’s device using strong cryptographic standards such as AES-256. In non-custodial apps, keys never leave the device unless explicitly backed up by the user.
Biometric and Multi-Factor Authentication
To prevent unauthorized access, wallet apps often integrate:
- Fingerprint authentication
- Facial recognition
- One-time passwords (OTP)
- Hardware security modules
Multi-factor authentication (MFA) adds a crucial barrier against compromised passwords.
Seed Phrase Backup and Recovery
Most non-custodial wallets generate a 12- or 24-word seed phrase during setup. This phrase serves as a master recovery key. Users must store it securely offline—preferably written on durable material and kept in a safe location.
[p]Improper seed phrase handling remains one of the most common causes of permanent asset loss.[/p]
Secure Transaction Signing
Before broadcasting a transaction to the blockchain, the wallet cryptographically signs it with the private key. Advanced wallet apps display detailed transaction information—including fees, recipient address, and network confirmation time—allowing users to verify accuracy before approval.
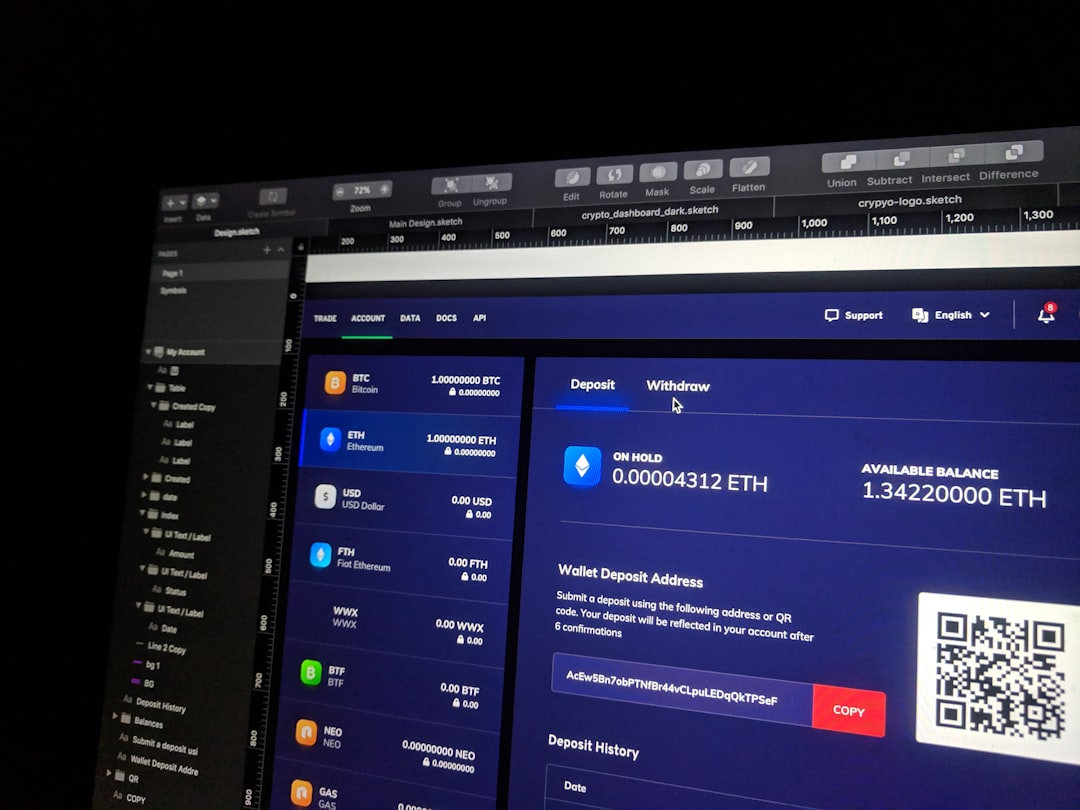
Transaction Integrity and Verification
Secure storage alone is not enough. Wallet apps must also ensure safe and accurate transaction execution.
Address Verification
Clipboard malware that replaces copied wallet addresses is a known threat. Reliable wallet apps integrate safeguards such as:
- Full address display for verification
- QR code scanning to reduce copying errors
- Address book whitelisting
Fee Transparency
Transaction fees vary depending on network congestion. A serious wallet application provides transparent fee estimation and allows users to adjust priority levels without obscuring cost details.
On-Chain Confirmation Monitoring
After broadcasting a transaction, the wallet tracks confirmation status directly from blockchain nodes. This visibility prevents confusion and reduces the risk of duplicate transfers.
Integration with Decentralized Applications
As decentralized finance (DeFi), NFTs, and Web3 services grow, wallet apps increasingly function as gateways to external platforms. Secure integration requires:
- Permission-controlled smart contract approvals
- Clear notification of token allowances
- Revocation tools for outdated permissions
Users should carefully review smart contract permissions before confirming transactions. Excessive token allowances can expose funds to avoidable risk if a connected application is compromised.
Risk Management Best Practices for Users
Even the most secure wallet app cannot compensate for poor security habits. Responsible asset management includes:
- Keeping software updated to patch vulnerabilities
- Avoiding public Wi-Fi when executing high-value transactions
- Using hardware wallets for long-term or large holdings
- Verifying URLs and application sources before downloads
- Never sharing seed phrases under any circumstances
Phishing remains one of the primary threats in the crypto ecosystem. Fraudulent emails and fake support channels frequently attempt to trick users into revealing recovery phrases. Legitimate wallet providers will never request such information.
Regulatory and Compliance Considerations
As digital asset markets mature, regulatory oversight is expanding globally. While non-custodial wallets typically operate without direct custody of funds, custodial providers may be subject to licensing, anti-money laundering (AML), and know-your-customer (KYC) regulations.
For institutional users or corporate treasuries, compliance features such as multi-signature authorization, audit logs, and transaction reporting become critical. Multi-signature wallets require approval from multiple parties before funds can be transferred, significantly reducing internal fraud risk.
Image not found in postmetaEvaluating a Crypto Wallet App
When assessing a wallet application, users should consider the following evaluation criteria:
- Open-source code availability and public security audits
- History of security incidents and response transparency
- Supported blockchains and tokens
- User experience and clarity of security prompts
- Backup and recovery documentation
Reputation and development longevity matter. Established wallets with consistent updates and clear communication policies are generally more dependable than newly launched, minimally reviewed alternatives.
The Future of Secure Wallet Technology
Innovation in wallet security continues to evolve rapidly. Emerging technologies include:
- Multi-party computation (MPC) to distribute key control across devices or entities
- Social recovery mechanisms that reduce reliance on a single seed phrase
- Hardware-secured enclaves within mobile devices
- Biometric cryptographic binding
These advancements aim to reduce single points of failure while preserving user sovereignty. In the long term, user experience and security are expected to converge, making secure self-custody more accessible to mainstream participants.
Conclusion
Crypto wallet apps are central to the safe participation in blockchain networks. They safeguard private keys, authorize transactions, and provide access to financial infrastructure that operates without traditional intermediaries. The strength of a wallet lies not only in its encryption but also in its transparency, transaction controls, and backup mechanisms.
For individuals and institutions alike, secure storage and responsible transaction practices are inseparable from successful digital asset management. Selecting a wallet should be approached with the same seriousness as choosing a bank or financial custodian. In a decentralized environment where users hold ultimate responsibility, informed decisions and disciplined security habits remain the most reliable defense.
